|
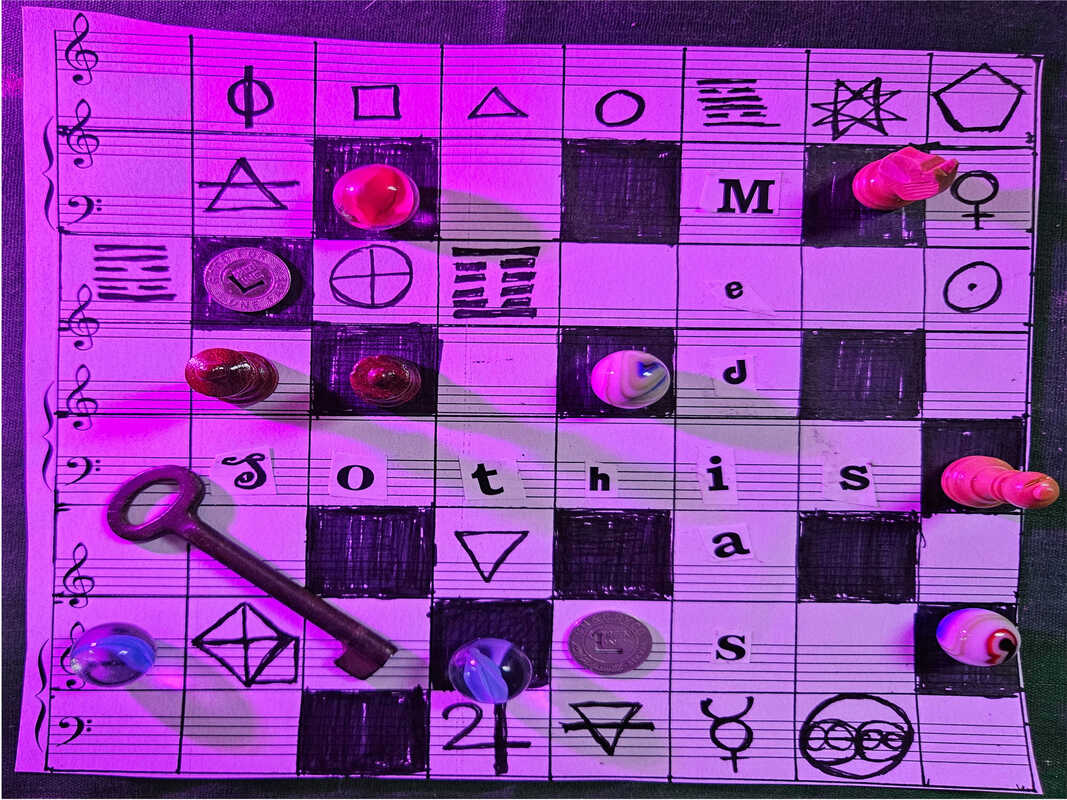
The term “dreaming in code” has entered into popular parlance among information and technology professionals as a way to denote those elite programmers who have so mastered their various software languages that they can “dream in code”. A hacker can write a script and inject it into cyberspace, altering the flow of information. By parallel a skilled worker of the Art Magical can utter their breath into the void and astral plane, altering the flow of imagination, becoming someone who “codes in dream”. This article looks at other parallels between the world of hackers and occulture in search of inspiration for the magical community.
THE VALUE OF OUTSIDE INFLUENCES (Cosmic or Otherwise) There is the danger in any field of endeavor to slip into a comfortable routine, to not seek the boundaries and push them, to play it safe and not experiment. In the arts this happens from following whatever is fashionable and trendy at the time; in the sciences from working around the pet theories of the day; in life from not pushing ourselves hard enough to see how we might expand our edges and do the better work of which we are each capable. This is no less true for magicians than anyone else. As much as occultists work towards self-realization, individuation, and mastery of the Art we are not immune from the trends circulating amidst our various esoteric communities. This is not to place a value judgment on any given trend, but a call to closely examine the reasons behind a trend, and the effects its adoption can have within oneself and the community. The dangers of following trends blindly are there just as much for the solitary practitioners who often look to books, articles, and internet sites as the basis for their practice, as to those who work in covens, lodges, and circles. Whether you are a solitary practitioner, work in a group, or some mixture thereof, tremendous sources of creativity and insight can be tapped, and utilized in the magical arts by taking a cross-disciplinary approach and researching what is going on in other fields of human endeavor. Does it matter if ones inspiration comes from the transplutonian mauve zone as opposed to an adjacent subculture? Either way outside influences remain essential sources of inspiration. While insulating oneself from outside influences can have the beneficial effect of strengthening inner resources, at other times those reserves need to be refilled and built up by looking into lines of work we are unfamiliar with. Delving into alternative lines of thought and thinking is very much akin to traveling and immersion in a foreign culture, or the new contacts we make when being of service to the inner worlds. Upon returning home we will find we have been changed, perhaps even transformed by our journey. If nothing else, we will come to appreciate the diverse approaches people have towards life and learn that the path we walk on is not the only path to walk on. At the same time we will perhaps develop a better understanding of the similarities people share beneath the surface appearances of different goals and aims. And then we can see where the paths come together and merge. It is in this regard that I wish to share my own voyeuristic love affair with hacker culture. In the course of my contemplation of the lovable bunch who spend their hours writing code, reverse engineering hardware, figuring out where systems are weak and security is lax, I came across a number of similarities between the communities surrounding hacking and esoterica. I have looked at our shared strengths and weaknesses and have noted some differences. From this exercise in analogical thinking I realized there are a number of activities and attitudes, as well as ways of approaching problems that occultists could adopt from the practice of hackers. [Further study also gave me ideas for a number of magical techniques inspired by hacking.] NOTES FROM A PASSIONATE OBSERVER As a student of the Western Mystery Tradition I write about hacking and hackers not as someone who has been deep on the inside of that scene, but rather as a passionate observer. I may be on the sidelines but I have had an ongoing fascination with the history, lore, and practices of hacking and phone phreaking since I was an adolescent. My own computer and technical skills are very average. What continues to draw me back to hacking is my own sympathy with many of the political and social aims inside the movement, their love of pranks, and long history of culture jamming. As a kid I was something of an amateur phone phreak. I knew a few tricks for making free calls on pay phones. A precocious reader, at a young age I’d zipped through Steve Levy’s Hackers: Heroes of the Computer Revolution and had gotten all excited about making further explorations of the electronic frontier via the telephone wires. It was around this time that I once got a hold of a phone lineman’s box. I didn’t steal it, just took it. The phone guy was nowhere around, but a piece of his equipment had been left at a switching box. When I figured out it had a modem and rudimentary computer in it I started using the device to connect to various BBS’ in the hopes of accessing further knowledge on any number of arcane subjects. Little did I know the box made a trace: anytime I placed a call the box also connected to the Cincinnati Bell office. One day while I was being subjected to a compulsory eighth grade education, an agent from the phone company came to the house, looking for me. He asked my mom where I was. When she told him I was at school, he asked if she had seen the lineman’s box, telling her that it had been traced to our address. My mom, always keeping a sharp eye on me, had of course seen me hooking it up to the phone line and quickly turned it over to the authorities. On that day perhaps, I was perhaps lucky to be at school. It probably spared me from a stern grilling from a telco agent. And although I didn’t pursue the path of active hacking and phone phreaking much further than that, my interest in it remained and I was later blessed to have close friends very savvy in this area. I started investigating hacker culture on a deeper level. I do this in several ways. The first is by reading 2600: The Hacker Quarterly on a regular basis. Some of the articles fly way over my head, especially those that involve dense coding. Others that are on such things as phone systems, amateur radio, satellites, GPS, subverting digital rights management, and basic security are suitable for the beginner. Something of a radio geek myself, over the past four years I’ve also been a regular listener to the two radio shows hosted by Emmanuel Goldstein, editor-in-chief of 2600, these being Off the Hook on WBAI in New York, and Off the Wall on WUSB in Stonybrook (both available archived online and as podcasts). The magazine and radio shows go together like bread and butter. Whereas the magazine provides practical articles, as well as perspectives from individual hackers in both a column and extensive letter section, the radio shows explore the social and political implications of technology. Apart from these sources there is a plethora of audio and video available from various hacker conferences, including the Chaos Communication Congress and H.O.P.E. (Hackers Of Planet Earth) to name just two. I absorb a lot of this audio material while at my day job or when doing home repair. I think it would be a good move if more of the occult oriented conferences and festivals archived all of their talks online as well. These would become tremendous resources after an event to be tapped by attendees who weren’t able to hear or see every presentation. It also gives those who didn’t go, whether by choice or circumstance, the gift of learning something new from the speakers. And it may inspire them to go in the future. More importantly, putting a talk online adds to the corpus of occult knowledge available to anyone with an internet connection. The magazine, radio shows, and talks from the cons got me very excited, and I thought about applying myself towards becoming a hacker. Because hacking is inspiring to me I decided to make some technological shifts in my life. But where would I begin? Up until the end of January in 2014 I presented radio programs for over a decade, first on a pirate station Anti-Watt and now on WAIF in Cincinnati. Despite having chosen to focus more of my efforts on writing, radio is still a medium I love. I had learned that many hackers are also Hams and have decided to apply myself towards receiving an Amateur radio license. I also decided to learn about Linux by running Oneiric Ocelot, a release of Ubuntu on one of my computers (perfect for someone who “codes in dream”). Learning a new Operating System is like learning a new system of magic. Routine tasks on a Windows system are now not quite as simple, but the mastery that comes from training, is in itself a source of pleasure. Open Source projects and software are also more closely aligned to my own personal values and ethics. HACKER CULTURE AND OCCULTURE: SIMILARITIES AND SYMPTOMS OF STEREOTYPE Though I have dipped my toes into the world of hacking, I am most passionate about occulture and those communities surrounding the ongoing magical revival. As I became more familiar with hackdom it was a natural step for me to notice similarities between these two camps and the places where their boundaries overlap. While the methodology utilized by hackers and operative magicians may seem to be in diametric opposition, their aims need not be so. At their core individuals in both movements seek to utilize their abilities to change and challenge themselves, and through magic, or manipulation of technological systems, change the world. The skill sets and ethics upheld by each have much to offer the other. Both hackers and occultists have also suffered from stereotypes that are striking in their similarity, and looking at them can suggest ways these stereotypes can be maneuvered around and disarmed. Weaknesses can be overcome, similarities built upon, and the strengths of one group borrowed for use in another to arrive at a new synthesis. The negative stereotypes in both communities come from stigma surrounding those who have used their skills, whether it be at hacking (hardware, software) or at practical magic (spells, hexes, talismans) for nefarious ends. People outside of these groups fear these abilities because they do not understand them. Distinctions between White Hat and Black Hat hacking find their parallels in Black and White magic. Many occultists and hackers however decry these distinctions. You are either a mage or not, a hacker or not. A person engaged in criminal computer activity is simply a criminal, and an occultist who puts hexes and curses on people needs to take a close look at their own values. Yet it remains a truth that curses are a part of magic, just as hacking for personal gain is taken up by technological adepts. However both magic and hacking can be used in the cause of Justice when the typical channels of law are insufficient or are themselves corrupt. Magicians and hackers both suffer from stereotypes that focus in on what is perceived to be “dark side” activities. The media has perpetuated images of pagans, witches, occultists and hackers as antisocial terrorist misfits, out to destroy society and brainwash your kids. But the corporate media aren’t the only people upholding this myth. The clandestine and elitist attitudes often ensconced within both the hacker and occultist scenes have served to reinforce perceptions created by the media that both groups are up to something illegitimate. OPEN SOURCERY Being “out of the broom closet” and transparent about our beliefs, activities and practices is one way to combat these negative stereotypes. This is akin to the way that technologists and desk jockey wizards’ share their techniques and programs in the Open Source Software movement, which allows users to study, change, improve and redistribute software code, that in other situations would have been kept hidden and proprietary. Joshua Madara, who is a key innovator doing much to explore the intersection between occultism and hacking, rewrote the traditional four Powers of the Sphinx as “To Know, To Will, To Dare, To Make Open Source” in a blog post he wrote on the subject of “Open Sourcery” . Groups like The Open Source Order of the Golden Dawn have also taken the values of the Open Source Software movement and applied them to magic. There remain groups and teachers who think it is best to keep information out of the hands of magical students, whether “for their safety” or so they can hold on to flimsy claims of power, and keep a person beholden to them. Magic and the Mysteries protect themselves, and those who are not ready for certain magical experiences or techniques will be blocked out by the beings of the inner world. Sure, there may be folks who can penetrate into a certain dangerous place in the inner realms, or use a technique to awaken their kundalini in an unsafe/unprepared way, and they will get blown up. From time to time to, a script kiddie may access something online that he wasn’t ready for and have the authorities called down on him. That doesn’t mean the information shouldn’t be out there. Hackers who expose secret information have been in the headlines for years now. Julian Assange’s Wikileaks project is just one high profile example. Other folks, like the people behind Cryptome have also been releasing important documents to the public. Luckily in the magical world some kind hearted souls have stepped up to the plate with the Watchers of the Dawn website to “keep an eye on the antics of occult groups.” Leaking magical secrets is a time honored tradition in magic itself. Besides serious errors in our ideas of the transmission of occult lineages (see Frater Acher’s wonderful posts on the Asiatic Brotherhood for more insight on this) mages have been ripping each other off for ages, Crowley’s publishing of the Golden Dawn material a prime example. John Michael Greer said in his talk, A Magical Education, “We know one thing for sure about magicians in the past— anywhere in the past: they used what worked. The oldest and most authentic tradition in all of magic is the tradition of stealing anything that’s not nailed down, and bringing along a crowbar for use on the things that are. Choose any magical tradition from the past, look into its roots, and you’ll find a fantastic gallimaufry of sources.” There is something to be said about working in secret, developing something clandestine, with a group or alone. But when the material reaches a level of maturity and strength, the results should be published or shared so that the rest of the community can get to experimenting and working with the material. WHATS YOUR HANDLE? As our communities have become more transparent and open we have been witness to the big strides taken in reclaiming such words as “witch” away from the negative connotations media authorities have imbued them with, just as the LBGQT community has done with the word queer. This is also true of the words hacker and hacking. A time-honored tradition among occultists and hackers is the practice of taking on a handle, moniker, or magical name, for instance Cap’n Crunch, the handle of John Draper, or Starhawk, the magical name adopted by Miriam Simos. The names we choose are used as a way of solidifying our identity with the movements and cultures we believe in. Choosing a name is an area where a person is able to show off their cleverness, creativity and distinguish themselves as well as show the areas of practice or subjects they are interested in. In my opinion a magical name or handle is a mixed bag. It can be quite fun and empowering to choose our own name, for names have power. On the negative side I see this trend as reinforcing the clandestine and elitist attitudes of these cultures, as these names serve to set an individual apart from the mainstream. I don’t see anything wrong with the practice per se, especially if the person is using it to remain anonymous and they work in a field that may persecute them. But it can be offsetting to those who would otherwise embrace our ideals. It is also good thing to stand behind being a hacker or occultist under our own given names, to show that there is no separation in our life – we are who we are, outside the ritual circles and away from the computer screen or soldering iron. Using your given name also is a good way to keep an inflated sense of self in check. THE HACKER ETHIC While part of the work of an initiate is to work with inner contacts and spirit beings, which can work to regenerate 21st century magical practice, lateral thinking and taking what has worked in other fields and subcultures, and applying it to the magic is another way to nurture the community. The principles of the hacker ethic in particular could be adopted by individual working occultists. These are looked at in brief below. SHARING & OPENESS: Publish your magical research and share your experiments, both the successes and failures. Advanced techniques should not be kept secret for the solo pleasures of XI degree inepti. To paraphrase Josephine McCarthy has said, “the idiots will blow themselves up!” while those who can put the information and knowledge to good use will have access to it. MISTRUST AUTHORITY, PROMOTE DECENTRALIZATION: While lodges, covens and groves will continue to play a role in the ecology of magical communities, an increasing number of workers are finding more fluid forms of collaboration to be desirable. People gather together when the work needs to be done, and disperse afterwards. Natural leaders and officiators may arise in such situations, but the work is bared and born by the group. When it is over, the workers return to their daily solitary practices and projects. The traditional groups magicians would find themselves in become networks of connection rather than bureaucratic hierarchies passing out merit badges when a successful banishing ritual is done. Though the priesthood may be decentralized over space and time we can all come together circling the flame of the inner convocation. WORLD IMPROVEMENT: Whether the improvements come from triggering the tides of death, destruction, and cataclysm, or through being a catalyst for growth, regeneration, or birthing, service should be the byword and guiding principle behind the work that is engaged in. Magicians are midwifes of life and death. They uphold civilization, whether in its upswing or decline. They go in from one job to another, not always knowing what will be required of them, and stretch themselves in the process, becoming more pliable for future jobs. They get on with the dirty jobs other folks in their right minds wouldn’t want to touch. Carrying the stillness within them, they show up.
0 Comments
Leave a Reply. |
Justin Patrick MooreAuthor of The Radio Phonics Laboratory: Telecommunications, Speech Synthesis, and the Birth of Electronic Music. Archives
July 2024
Categories
All
|
 RSS Feed
RSS Feed
